Aligning business goals with security imperatives
Aligning business goals with security imperatives
Many organizations have spent massively on cyber security, both on tooling and personnel. Today, some feel the need to cut back. In that sense, the cost of security has become a major focus— perhaps as much as security itself. In an effort to manage costs and ensure that business and security priorities are aligned, companies are automating significant portions of their cyber functionality by putting digitized cyber risk management processes in place to ensure they ladder up to the organization’s top-line operational and business strategies.
The landscape as we see it
In reviewing many risk models, we find the concept of business-driven risk scenarios to be lacking. The viewpoint of the business needs to go hand-in-hand with the viewpoint of the cyber security team and that is not the case at enough organizations. The identification of these risk scenarios should be led by the business.
And the process would be much more effective if it were informed by a model that enables business leads to better understand the impact security controls may have on those risk scenarios. Many companies don’t get that insight consistently, making it challenging to formulate a fluid ongoing relationship between the controls and the business.
In the cyber community, we try to plan for worst-case scenarios, but many incidents happen in relative obscurity and are not earthshattering, let alone business-shattering. From that perspective, we see many companies working to embed security, not only within the second line of defense, but within the more operationally focused first line as well as the audit-driven third line.
Larger organizations have spent, over the last 10 to 15 years, big money on IT security. Now they are acknowledging that they need to develop a new model focused on lowering costs through an automated approach to security and putting the right people in the right roles.
What we believe you should do about it
Think holistically about where you need to invest. Consider what risk scenarios need to be in place, and what controls are most relevant. Most companies are now engaged in a digital transformation, which suggests they should also explore automating their cyber and risk management processes.
Many incidents would be quite easy to detect if security policies and controls were embedded in the business. Bottom line, companies are encouraged to integrate cyber security across all three lines of defense, rather than operating in silos.
Make security an end-to-end priority. The foundational action is to establish an ongoing dialogue between the security organization and the rest of the enterprise to ensure security is in sync with the business in terms of strategic and operational planning. To that end, implement engineering approaches—such as secure by design and privacy by design—that are intended to introduce security into the daily mindset of the DevOps team as they craft new applications and services.
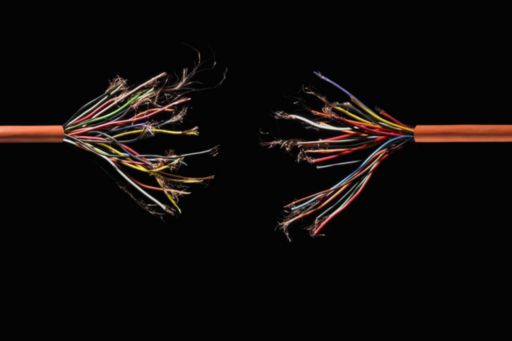
Ultimately, we’re hoping to see cyber security professionals move away from being perceived as an IT-driven function. As such, the cyber team needs to be business-led and business-aware. Otherwise, that symbiotic handshake between business and cyber is never going to solidify.
The excerpt was taken from KPMG article, All hands on deck: Key cyber security considerations for 2020”.
© 2024 R.G. Manabat & Co., a Philippine partnership and a member firm of the KPMG global organization of independent member firms affiliated with KPMG International Limited, a private English company limited by guarantee. All rights reserved.
For more detail about the structure of the KPMG global organization please visit https://kpmg.com/governance.